Identity & Access Management (Keycloak) – IDC Lab
Overview
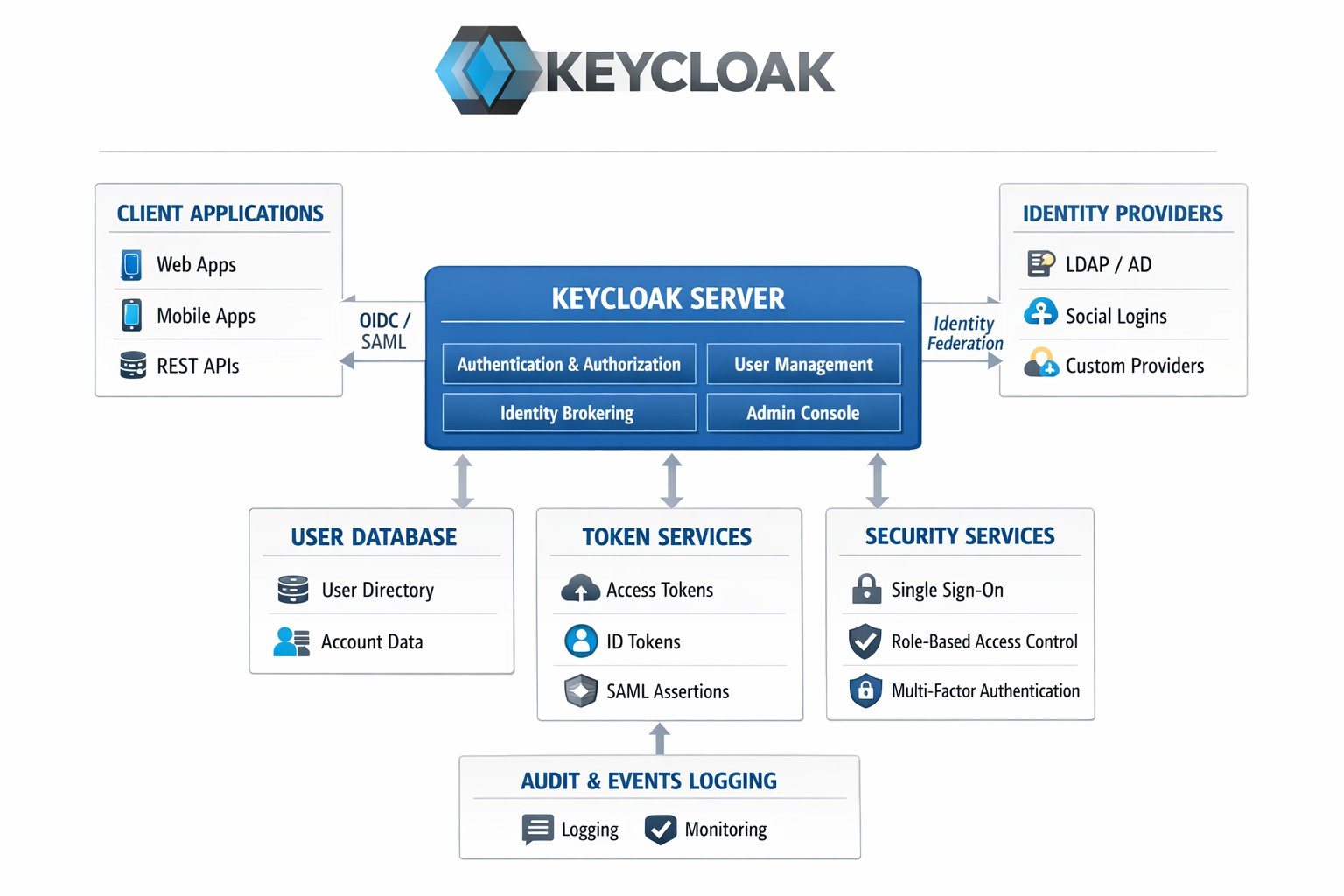
The IDC Lab utilizes Keycloak as a centralized Identity and Access Management (IAM) platform to deliver secure, scalable authentication and authorization across applications and services. Keycloak provides a unified identity layer with support for industry-standard protocols such as OAuth 2.0, OpenID Connect, and SAML, enabling single sign-on (SSO), role-based access control (RBAC), and centralized user management. This approach ensures continuous security validation, centralized access governance, and reduced attack surface across the IDC Lab environment.
Keycloak IAM Objectives
o Centralized authentication and authorization for all applications and services.
o Enforcement of Zero-Trust access through explicit identity verification.
o Single Sign-On (SSO) to improve user experience and access control.
o Role-based and policy-driven access management (RBAC).
o Secure service-to-service authentication using standard protocols.
o Centralized user, role, and credential management.
o Integration with DevSecOps pipelines for consistent security enforcement.
Standards & Protocols Supported
o OAuth 2.0 – Secure authorization framework.
o OpenID Connect (OIDC) – Modern authentication layer.
Keycloak is integrated with applications hosted in the IDC Lab to:
o Enables seamless user login across multiple services.
o Enforces access control based on user roles.
o Improves security through centralized identity governance.
o Simplifies application onboarding to the IAM platform.